We all know nowadays Internet-connected co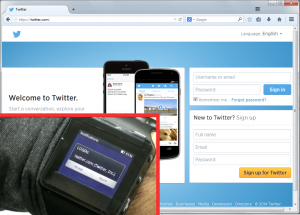 computers are not secure anymore: every day new viruses, key-loggers and stealth malware are created and spread. Besides that, when using the Internet we still keep sharing our most sensitive data with our insecure computers: our web passwords. Also we’re all having a bad time trying to remember many long passwords for different sites. Not any more with our technology. The Identiva PassKey is a tiny wireless device that allows people (like you, me and your grandma) to authenticate against any website in the world as simple as taping the device.
computers are not secure anymore: every day new viruses, key-loggers and stealth malware are created and spread. Besides that, when using the Internet we still keep sharing our most sensitive data with our insecure computers: our web passwords. Also we’re all having a bad time trying to remember many long passwords for different sites. Not any more with our technology. The Identiva PassKey is a tiny wireless device that allows people (like you, me and your grandma) to authenticate against any website in the world as simple as taping the device.
The PassKey logins to your favorite websites using the stored passwords (that are never revealed to your browser computer, just to the website), achieving an unprecedented level of security without requiring any change in the Internet authentication infrastructure. We have prototypes already working for the major websites. See it in action:
Traditional password managers are designed to be used only on trustworthy computers. You cannot securely plug your pendrive containing your password list on a Cybercafe computer, without risking your digital identity and digitally controlled assets. Sometimes, you should assume your password has been compromised as soon as you type it on an untrusted keyboard. The Identiva PassKey is the only device that allows you to log in using any untrusted computer with high security and no risk. And also, it is compatible with any password-enabled website in the world.
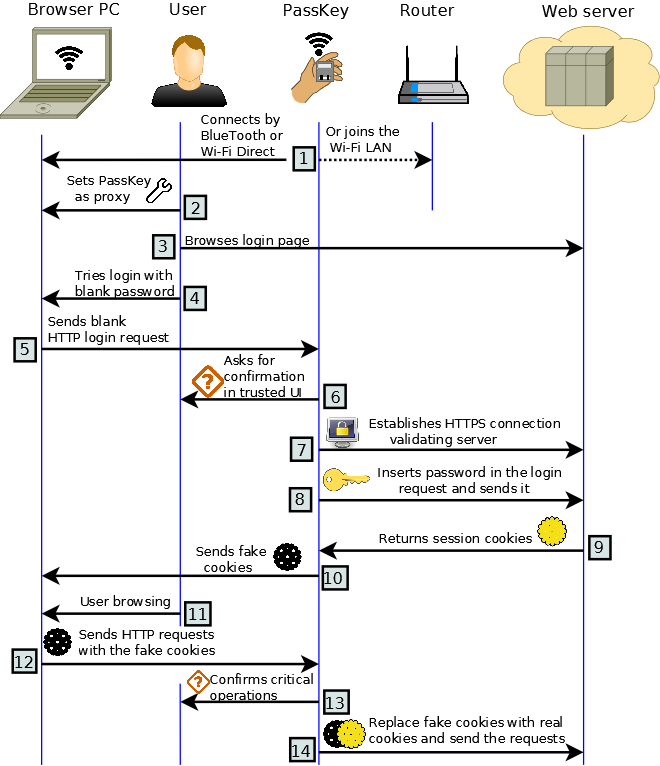
The following diagram shows the inner workings of the PassKey and the login and browsing flowchart:
The PassKey stores and handle all your passwords in a super-secure way and is able to feed the password to any existing password-enabled Internet website, such as your bank or your favorite e-mail provider, without ever disclosing the password to your mobile or PC computer, or to any hacker in the net. You will never have to worry again about your computer being infected with malware or about typing your password in a friend’s computer. Behind the scenes, the PassKey establishes a secure connection with the Internet server and only after checking the server authenticity it sends your password encrypted to the server. And afterward, the PassKey delegates Internet browsing to your favorite web browser running on a possible insecure environment. Also, at any time you are able to securely log out, leaving no authentication information on the untrusted computer.
For secure-critical operations, such as changing a password, updating your personal data or making a bank transaction, you’ll be able to configure the PassKey to require specific confirmations. Your can use your PassKey today, because it is compatible with all your favorite websites like no other authentication system. Having a simple user interface with a single confirmation button makes the PassKey login process secure, easy and natural.
Every Internet user in the world is a potential Identiva Customer: children, teens, adults, professionals, security personnel, and elderly: no one wants their digital persona to be hijacked and abused. The more the technology becomes Internet-enabled and pervasive, the harder the manual handing of passwords becomes.
The proof-of-concept hardware/software platform used for testing was a wifi-enabled smart-watch running the Android operating system and adapted for being able to simultaneously run a GNU/Linux distribution. The software was implemented in Python. For the production device, we will target a single-purpose security-hardened hardware platform such as a secure micontroller, which will just require adding a display, buttons and the battery. Also the PassKey supports password backups in the cloud. The requirements for the cloud servers are simple to met since the password backup service can be implemented on all of the standard web development languages, platforms and frameworks. We plan to make all the software open source for ease of auditing.
The Identiva PassKey wireless device concept was fully implemented and tested using a smart-watch platform. Nevertheless we plan to increase its security by using a single-purpose low-cost, power-efficient computing platform, such as as one based on a secure microcontroller or IoT board. The platform must have a Wi-fi and/or blue-tooth connectivity, an LCD display, a battery and a simple user interface having two confirmation buttons.
The core computing operations performed by the device are storing a password database, opening secure connections to external websites (or the computer) using the SSL/TLS protocol suite, verifying authentication certificates, and sending passwords in encrypted form. Also the PassKey is able to intercept the traffic between the untrusted computer and the website and provide the authentication tokens when needed, without disclosing them. Last, the PassKey can offload downloading or uploading large files to the untrusted computer without disclosing sensitive information, to preserve the device battery life. These operations are performed by a single software component that resides in the PassKey. On the computer side, the PassKey requires a simple two-step configuration process that does not require administrative privileges and involves configuring the PassKey as an Internet proxy and installing a root certificate provided by the PassKey. An optional user-mode software component can be run on the untrusted computer to multiplex Internet streams and reduce the CPU-load of the PassKey, increasing its battery lifetime.
The Identiva business model is to develop, promote and sell the product massively in every country of the globe. Our plan is to partner or license our technology to a company capable achieving economy of scale to bring the product to market under USD 50 a piece. Since our solution does not require any change in the Internet authentication infrastructure, we do not require special partnerships with web giants. Nevertheless we expect interest from main Internet companies in our technology since it reduces their identity fraud risk.
The device is designed to be implemented mainly on a Smart-watch, in augmented-reality glasses or as a key-chain accessory.
The innovations are protected by patents pending in US and Europe.
Like it ? Give us a “Like” in the Hack-a-day contest!